How AccuKnox and Rafay Systems Integration Can Help You Achieve Cloud Native Security
A comprehensive guide to securing your cloud native environments with AccuKnox Zero Trust CNAPP (Cloud Native Application Protection Platform) powered by Rafay Systems, the leading Kubernetes management and operations platform.
Reading Time: 6 minutes
Table of Contents
Cloud-native application protection platforms (CNAPPs) are a unified and tightly integrated set of security and compliance capabilities designed to secure and protect cloud-native applications across development and production.
Market Need for CNAPP (Cloud Native Application Protection Platform)
CNAPPs consolidate a large number of previously siloed capabilities, including container scanning, cloud security posture management, infrastructure as code scanning, cloud infrastructure entitlement management, runtime cloud workload protection and runtime vulnerability/configuration scanning. By 2025, 60% of enterprises will have consolidated cloud workload protection platform (CWPP) and cloud security posture management (CSPM) capabilities to a single vendor. Gartner, March 2023
Kubernetes has seen tremendous growth and maturity since its inception almost a decade ago, introducing a new era for modern software deployment and management.
Market Need for Kubernetes Management and Operations
According to the CNCF, Kubernetes is continuing to grow and reached its highest level ever, with 96% of organizations using or evaluating Kubernetes. This growth in adoption underscores the need for effective Kubernetes management and operations solutions. In an effort to standardize and govern the use of Kubernetes, 76% of high-performing organizations have created platform teams. However, growing pains—such as complexity, tool proliferation, skills gaps, cost, security and compliance—still remain, creating demand from platform teams for a better approach to Kubernetes management and operations.
The blog outlines the benefits that organizations can derive from AccuKnox and Rafay Systems, category leading Zero Trust CNAPP and Kubernetes Management platform respectively.
With the increasing adoption of modern cloud infrastructure and applications, cloud security services have become an imperative.
Cloud environments today are complex and distributed; they share resources across multi-cloud and therefore visibility and security enforcement can be a challenge. Although major hyperscalers like AWS, Azure, or GCP do provide basic security, they rely on a shared responsibility model. The tenant (end customer of cloud services) has the ultimate responsibility for protecting their own workloads and assets against zero-day attacks and advanced threats.
Modern applications running on Kubernetes are complex and enforcing security requires a deep understanding of access privileges, workload isolation, pod level hardening and firewalling.
Due to the highly ephemeral and transient nature of Kubernetes and micro-services, the compromise of a single pod could lead to cascading attacks.
Some of the most recent attacks at the modern workloads running in production are captured below:
The common thread to all of these is the fact that these are not simple attacks. These involve advanced threat vectors like East-West/Lateral Movement, Privilege Escalation, Secrets/Service Token hijacking, supply chain attacks, etc.
These attacks could be generated as early as developing code without following security best practices, hardcoded secrets, common CVE, 3rd party dependencies in open source, supply-chain attacks, vulnerable images which are exploitable and exposed at runtime. John Kindervag, a cybersecurity researcher, who coined the term “Zero Trust” in 2010 said, “ Never trust, always verify.” In the “perimeter-less” world we live in, there is a compelling need to implement Zero Trust Cloud Security solutions.
AccuKnox CNAPP (Cloud Native Application Protection Platform) provides Zero Trust security by auto-discovering application behavior and automatically generating Zero Trust “White List” policies. It also recommends hardening policies based on best practices industry standards such as MITRE, NIST, and CIS. AccuKnox achieves robust and frictionless Runtime security by the following mechanisms:
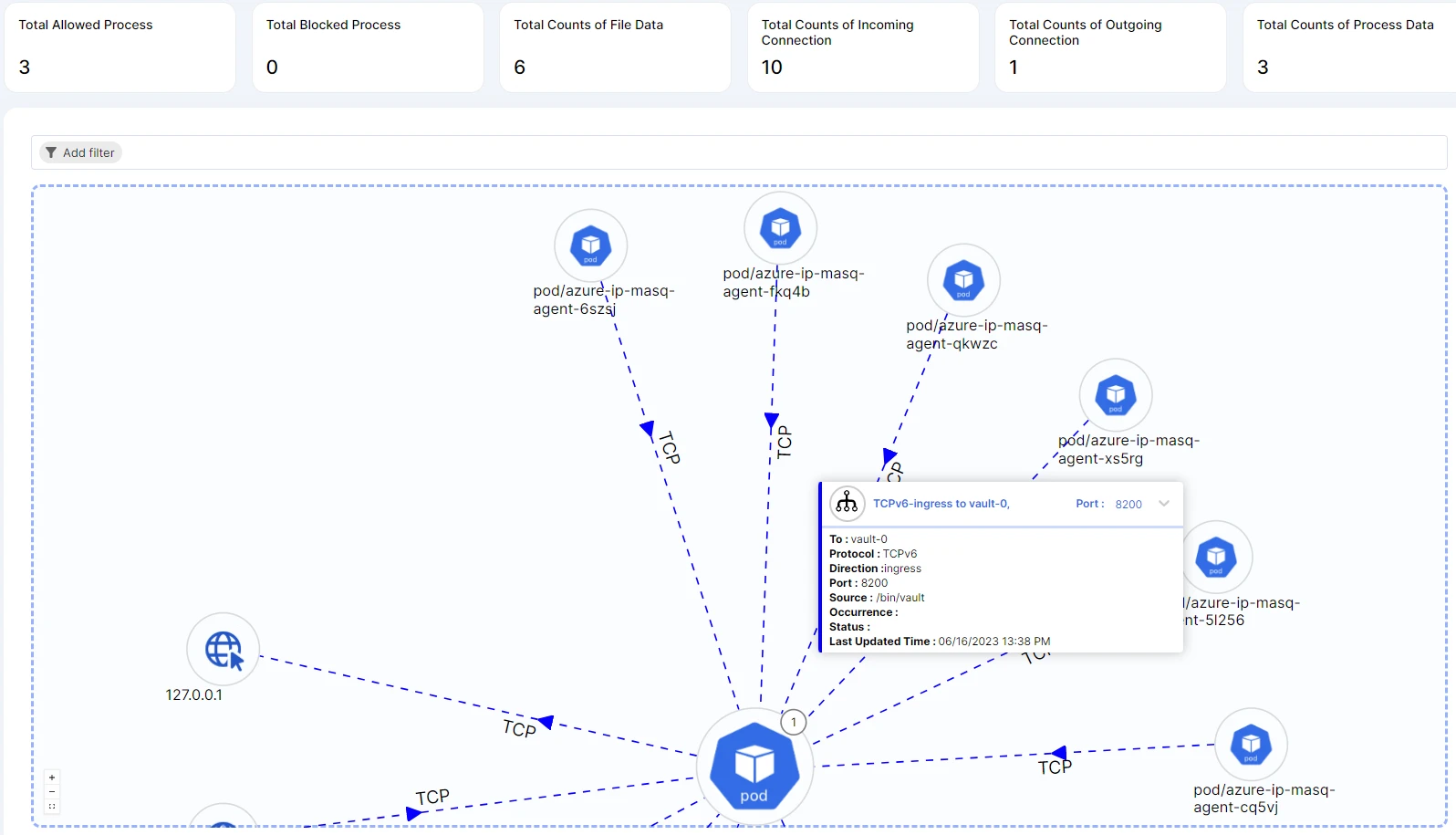
- Observability of the application is achieved by KubeArmor, Kubernetes Run-Time Security Engine, an open source Cloud Native Computing Foundation (CNCF) sandbox project. KubeArmor leverages the industry’s most efficient and popular kernel observability engine, eBPF (Extended Berkeley Packet Filter) and generates rich alerts/telemetry events associated with the container/ pod/ namespace. As they say, “You cannot secure what you don’t see.”
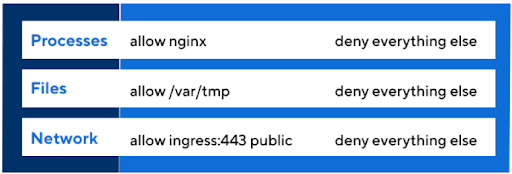
- While observability is important, an efficient and effective enforcement mechanism is equally important. If you stop the attack after it has affected one of your clusters in application, then it is a false sense of security: “A day late…A dollar short,” as they say! True Zero-Trust security allows what is legitimate traffic and denies everything else. This is achieved using KubeArmor. KubeArmor restricts application behavior (such as process execution, file access, and networking operations) of pods, containers, and nodes (VMs) at the system level. Enforcement is done by leveraging Linux security modules (LSMs) such as AppArmor, SELinux, or BPF-LSM to enforce the user-specified policies at the kernel level.
Companies are at varying stages of their transition to the Cloud and practically all of them have a combination of Public Cloud, Private Cloud, Hybrid Cloud, etc.
This complex deployment model and elastic scaling model makes tracking and enforcing of these security controls very difficult. This calls for a need to use a centralized security management platform, automate security tasks, and have a risk-based prioritization.
Rafay has a unique and differentiated ability to manage complex Kubernetes environments. This coupled with AccuKnox’s Zero Trust security capabilities provides organizations with a comprehensive DevSecOps-led security platform to address current and emerging threat vectors.
AccuKnox for KubeArmor is now a part of Rafay Kubernetes Operations Platform (KOP), and also a part of Rafay’s partner add-on catalog. One can optionally choose to deploy AccuKnox KubeArmor through Rafay’s Cluster Blueprint feature documented as AccuKnox recipe.
Organizations can now install AccuKnox KubeArmor to their existing running cluster and they can also have this as a custom add-on onto new clusters as and when they are spun.
Once AccuKnox KubeArmor is deployed, you will be able to have deep visibility into the workload which is empowered by eBPF and you can observe through Cloud Workload Inventory view. Upon onboarding cluster, it will additionally auto-discover your application behavior and recommend granular Zero Trust security policies control as categorized below:
By default, Kubernetes clusters are not segmented, allowing all pod communication and lateral movement. Hence the need for defining network ingress and egress control to ensure workload isolation, application firewalling, kernel hardening and micro-segmentation.
Additionally, your application security posture is detected and will be recommended hardening policies out-of-the-box based on MITRE, NIST, CIS, STIG, etc., security best practices. This will greatly reduce the “blast radius.”
AccuKnox can provide compliance, defining baseline, Kubernetes identity and entitlement management, compliance benchmarking, and governing of your dynamic application drift through GitOps version control workflow. AccuKnox fortifies the workload and helps achieve a true Zero-Trust posture of your application with guaranteed protection from Zero-Day attacks.
Rafay and AccuKnox provide consolidated security visibility into all kinds of virtualized applications for operations and security management. From post-attack mitigation to real-time defense, experience unrivaled security for your workloads with AccuKnox’s help to achieve resilient Zero Trust architecture. This helps the organization focus on growth, innovation, and delivering business value, while AccuKnox and Rafay deliver security and operations management, respectively.
About AccuKnox |
About Rafay |
Advanced Security for Workload on Containers/VM
Software Supply Chain Security
Cloud Infrastructure Security
|
Security
Governance
Integration
Operations
|
Value Proposition for Customers |
|
AccuKnox integration with Rafay provides your cluster with the following competitive edge over any other solution:
|
|
Don’t miss out on the opportunity to try Rafay, a one-stop solution to provide security, performance and visibility for enterprise and platform teams across organizations. Sign up for a free trial today and see for yourself!
Must read articles
- Zero Trust (ZT) – The Future of Cloud Security
- Zero Trust (ZT) Architecture, Framework and Model
- Cloud Security Governance, Risk and Compliance (GRC)
- How to Pick the Right CNAPP (Cloud Native Application Protection Platform) Vendor
- What is Driving the Need for CSPM (Cloud Security Posture Management)
- Agent vs Agentless Multi Cloud Security
Zero Day Attacks cost $3.9M on average

4+
Marketplace Listings
7+
Regions
33+
Compliance Coverage
37+
Integrations Support

Stop attacks before they happen!
According to the latest IBM cloud attack report - Each cloud attack on an average costs $3.92M
Total Exposed Attacks in 2024 Costed